The Seed Phrase Is Not the Problem. The Spectrum Is.
A reader asked how Concordium can remove the seed phrase as a user adoption blocker without compromising security. The framing of the question already contains the answer's difficulty. You cannot remove the seed phrase without trading something for its absence. The real question is what you are willing to trade, and that is a spectrum.
1 The private key, the seed phrase, and the confusion between them
Two things need to be separated before any recovery argument makes sense.
The private key is the cryptographic object that signs transactions. It is what authorizes movement on the account. The seed phrase is a human-readable backup from which the private key is derived. The seed phrase is not itself the authorization anchor. It is the recovery path for the anchor.
On Ethereum, Solana, Bitcoin, and nearly every other public chain, the private key is the only thing standing between a user and their account. Lose the private key, lose the account. The seed phrase exists because something has to back up the private key, and the chain itself provides nothing that can. The burden of preservation and recovery falls on the user. That model is unreasonable for consumers and impossible for AI agents, which will soon hold accounts at scale.
"Removing the seed phrase" therefore means one thing: finding a different way to recover the private key when the user's device or access is lost. Every industry answer to that question sits somewhere on a single spectrum.
2 The custody continuum
Every recovery system sits somewhere on a custody spectrum.
At one end, the user holds the seed phrase alone and shares it with nothing or no one. The account cannot be taken. It can be lost permanently if the phrase is lost. Full sovereignty arrives with full fragility.
At the other end, a third party holds everything. Recovery is as simple as a password reset. Custody has been surrendered. The convenience is high precisely because the dependence is high.
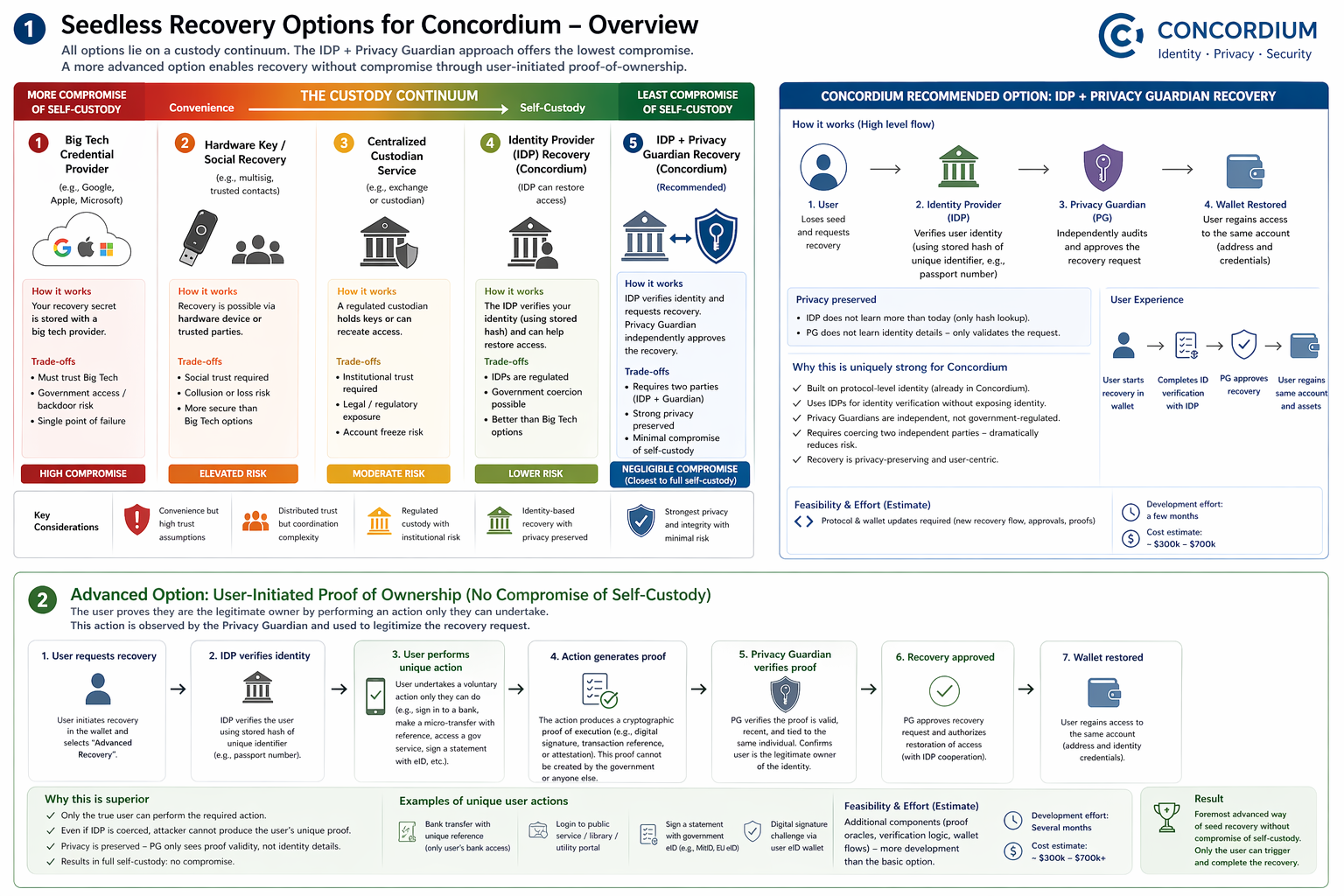
Every seedless design in the market sits somewhere on the continuum between these two ends. The chart below places the industry's main seedless design principles along that axis.
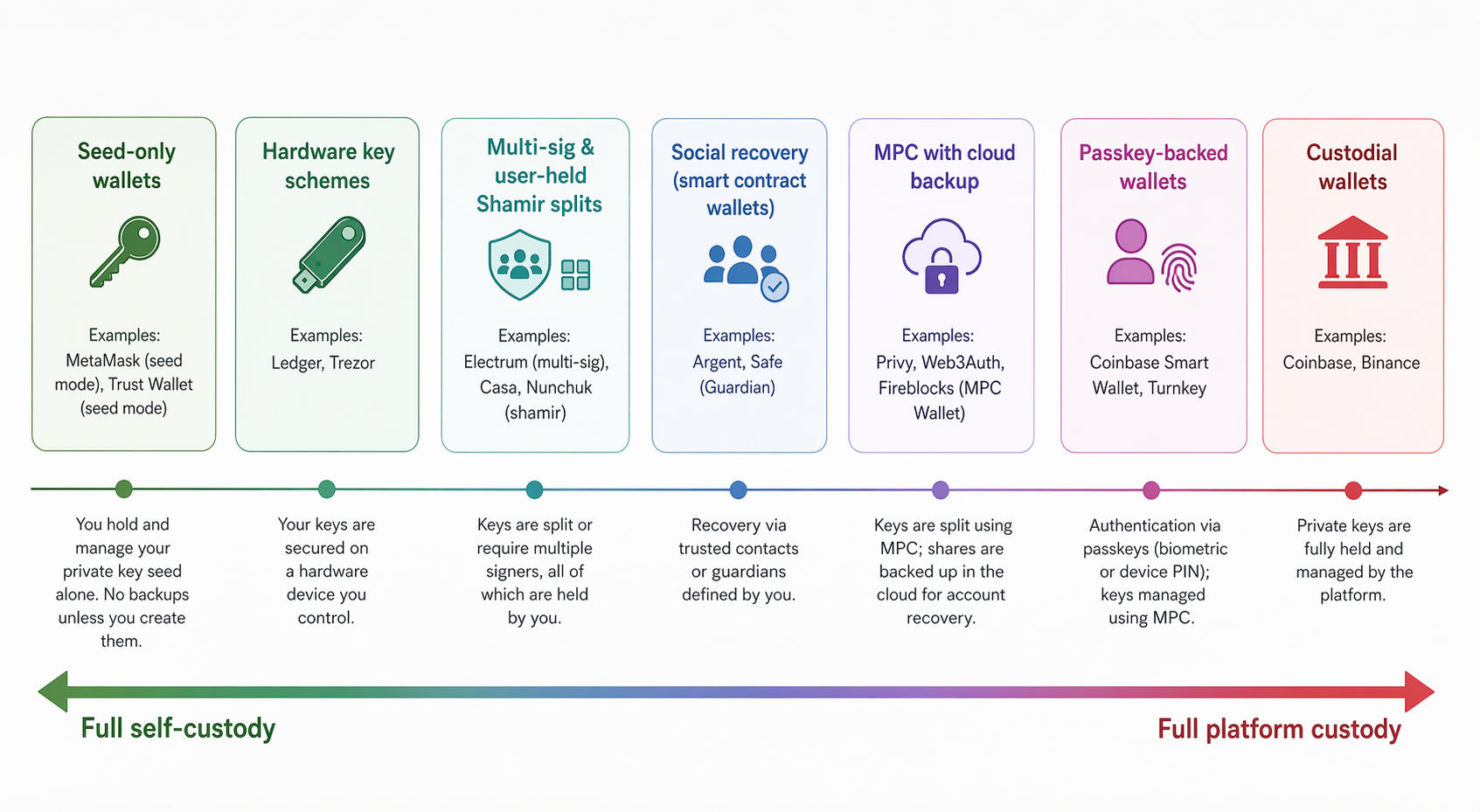
Between the poles sit the industry's many attempts at seedless recovery: custodial wallets, social recovery, cloud-backed MPC, passkeys tied to major platforms, multi-signature arrangements, hardware-key schemes, and hybrids of every kind. The interfaces differ more than the underlying logic. Each sits at a different place on the continuum, determined by how much of the burden remains with the user and how much is transferred elsewhere.
Concordium could quickly participate on the spectrum by shipping an application-layer recovery that backs up seed material to iCloud or Google Drive, encrypted with a platform-tied key. This would require no protocol work and could be available very quickly. But it would also place a tech giant in the recovery path, with all the custody trade-offs that implies. For retail users entering crypto for the first time, this might feel like the right product, but it would not be Concordium-native in any meaningful sense, and it would be a significant platform-based concession of custody.
This highlights the mistake in the market's framing. Seedless recovery is often presented as innovation when it is really no more than relocation. The seed phrase disappears from sight while the custody trade-off remains exactly where it always was.
3 The logical binary trap
The obvious next thought is that a chain with a built-in identity layer, like Concordium, could use the identity to authorize recovery directly. However, that intuition quickly runs into a logical trap.
Any seedless design that leans on a single credential, whether a social login, a biometric scan, or a verified identity, faces an unavoidable binary.
- A) If that credential alone can unlock the account, then whoever holds it is a custodian in different clothing.
- B) If the credential alone cannot unlock the account, a second factor is needed, and the user must preserve that factor, which reintroduces the exact same problem the design was originally meant to solve.
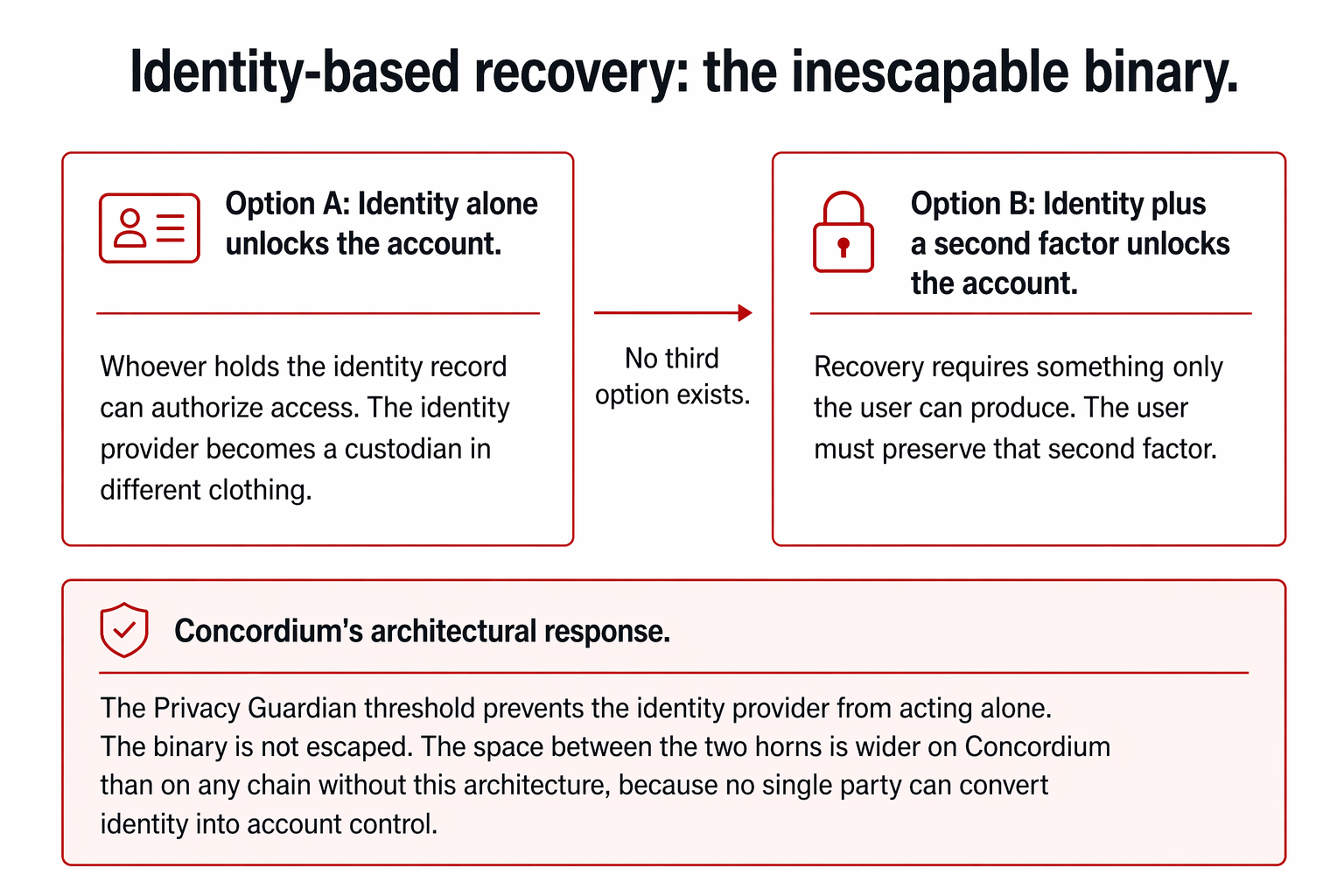
Existing credential-based recovery systems let the credential alone unlock the account. The credential might be a social login, a biometric scan, or a platform passkey. The pattern is the same: the service holding the credential becomes the custodian. The user never realizes they have handed custody over.
4 Concordium's two paths
Concordium possesses a unique combination of primitives from which better recovery systems can be built. Identity exists at the protocol level rather than as an external add-on. Verified users are introduced through identity providers. Independent Privacy Guardians exist as threshold authorities designed to prevent sensitive powers from being exercised unilaterally. Authority is thereby already inherently separable inside the system.
These unique properties make more robust recovery solutions feasible. Two distinct and superior recovery models can be derived by capitalizing on the properties.
4.1 Path one: distributed authority
The first path uses the identity provider and the Privacy Guardians together. Under such a design, the identity provider would confirm that the claimant is the verified person originally attached to the account. The Privacy Guardians would participate through a threshold process that prevents the identity provider from acting alone. Recovery authority would therefore be divided across independent participants rather than concentrated in one intermediary.
This does not escape the binary, but the compromise is smaller than in any single-credential design, because two independent parties must be coerced separately. The Privacy Guardians, unlike the identity provider, are not government-regulated entities, and their raison d'être is to protect privacy and integrity. Coercing them is structurally much harder than coercing a regulated identity provider.
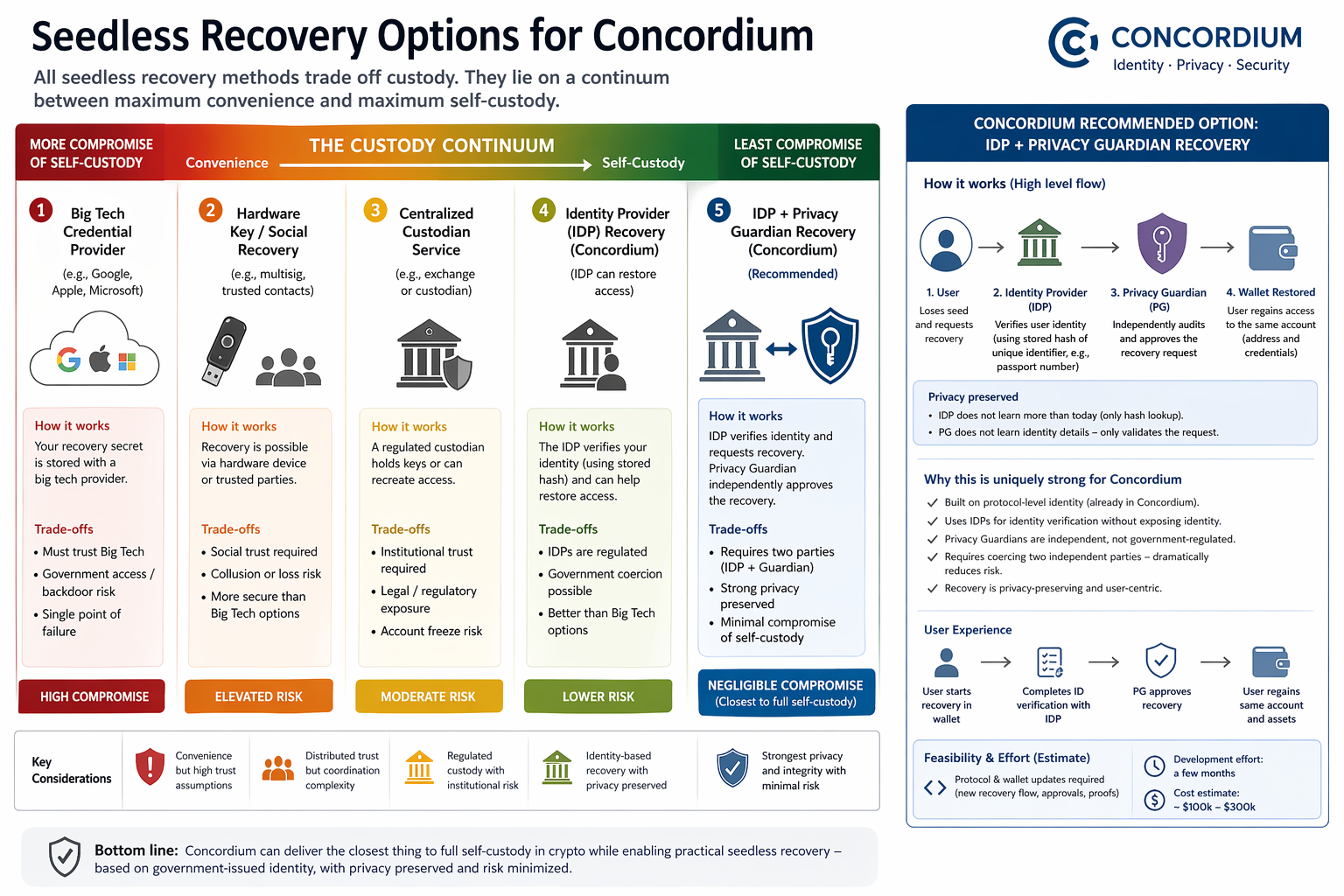
While this path does not constitute an escape from the custody spectrum, it is clearly the strongest visible position within it.
4.2 Path two: proof of present control
The second path adds a step that does escape the binary. The second model is more interesting because it challenges the hidden assumption inside the binary trap. That assumption is that if one credential is insufficient, then the missing element must be a secret stored in advance: another key, another device, another dependence the user must preserve indefinitely.
But given Concordium's unique properties, the missing element need not be something preserved. It can be something proven.
When recovery requires the user to demonstrate active command of their identity at the moment recovery is requested, the structure changes. The user would not merely be identified as the person tied to the account. The user would prove present control of that identity through a live mechanism only the rightful holder can invoke. A signed statement via national eID. A bank transfer with a specific reference. A login to a public service that generates a verifiable proof.
The trade-offs between the four candidate actions:
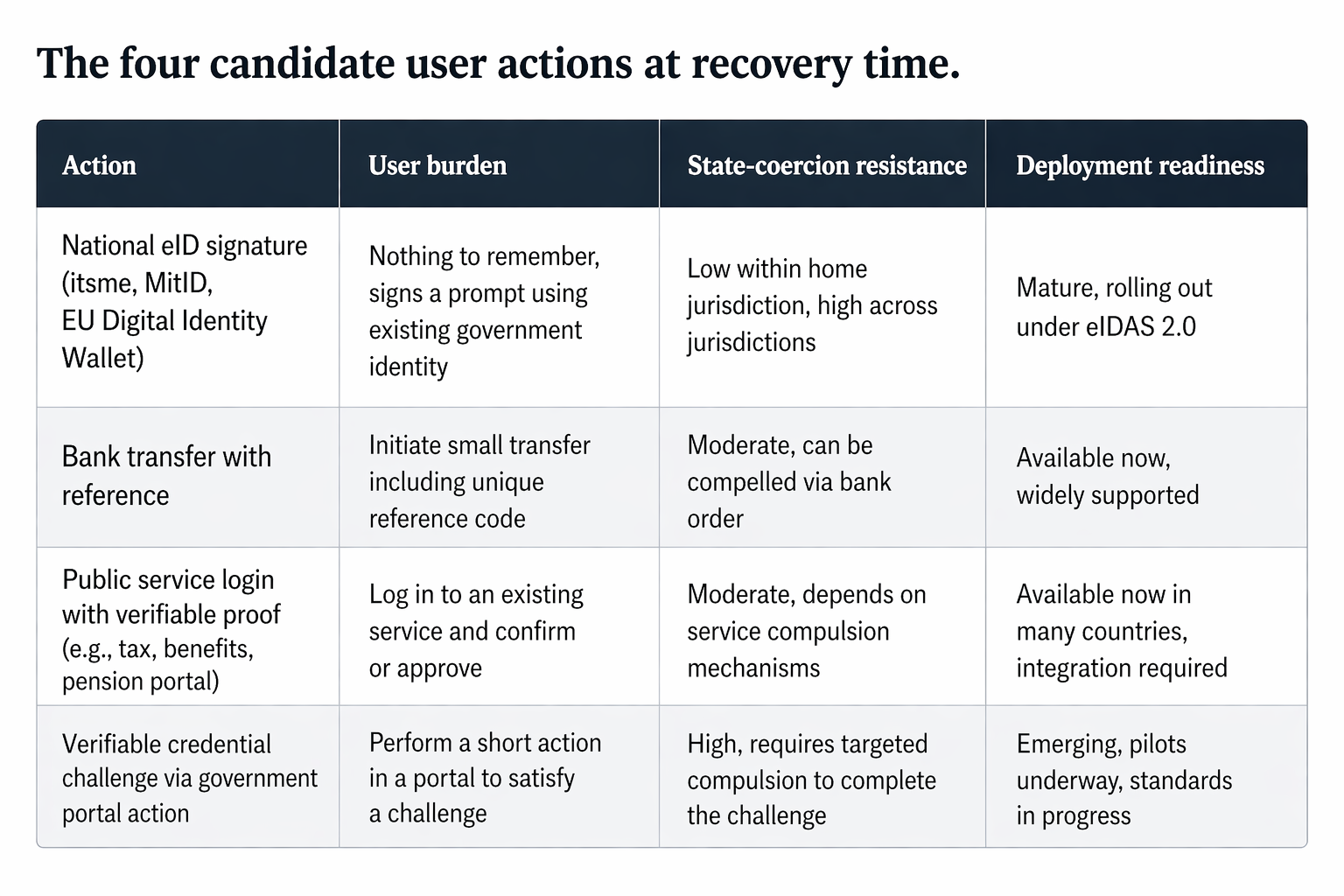
The Privacy Guardian observes that action and uses it as the final condition for authorization:
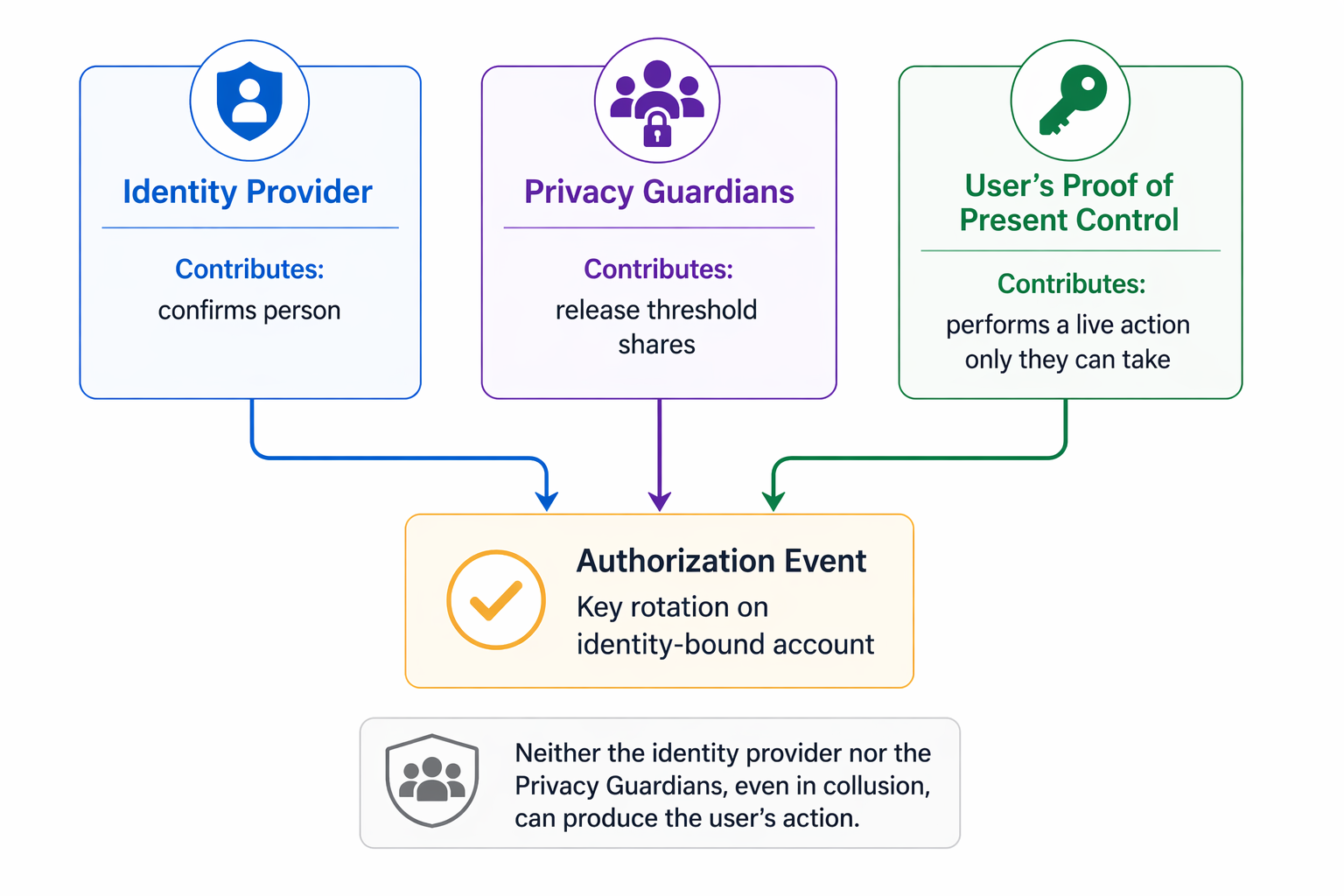
This is the abstraction that allows Concordium to escape the binary continuum of self-custodial compromises.
5 The coercion limit
No recovery system can fully resist a state capable of compelling every participant in the recovery path. A distributed model raises that bar; it does not remove it. The only arrangement that fully removes coercion risk is the one in which no recovery exists at all.
This is the uncomfortable truth beneath wallet UX debates. Every recovery path is also, in principle, a coercion path. Users who want absolute sovereignty must accept absolute fragility. Users who want recoverability must accept that some route back in exists under sufficient pressure.
Concordium's importance is not that it abolishes this trade-off. It is that its architecture allows the trade-off to be designed with more honesty than systems built around unilateral custodians or platform dependency.
6 The answer
The seed phrase was never the problem. It was the load-bearing beam of a model that placed nearly everything on the user.
Much of the industry has tried to hide that beam, repaint it, or move it elsewhere.
Concordium is interesting because it may allow the structure itself to be redesigned: first by creating the least compromised recoverable position on the existing spectrum, and later perhaps by moving beyond the old binary altogether.
That is a more serious ambition than making recovery feel easier.
It is the ambition of making recovery make sense.